In previous part , we discussed about protecting CQ5 author instance when CQ5 acts as a service provider (SP). In this blogpost, we’ll cover how to protect any published resource/website. We’ll be using Shibboleth SP for the same.
Necessary Steps :
- Installing LDAP Server.
- Installing Shibboleth IdP.
- Installing Apache tomcat on Ubuntu.
- Configuring Shibboleth IdP.
- Installation of SP.
- Make Apache aware of shibboleth
- Configuration of Shibboleth SP and providing it to IdP.
- Protecting and accessing the CQ published resource.
Steps 1-4 have already been covered in Part I. Subsequent steps are explained below :
-
Installation of SP
Installing SP and it’s configuration was a bit difficult task for me as the existing documentation was not very clear. I would like to mention few important points and brief the installation steps below .
-
Installing Apache2
sudo apt-get install apache2
-
Installing Shibboleth SP
Easiest way to install SP is via command line.
sudo apt-get install libapache2-mod-shib2 shibboleth-sp2-schemas
When the installation is completed, various components of Shibboleth will be placed in appropriate directories based on the OS file system layout. You may check:
- Shibboleth configuration files will be placed at
/etc/shibboleth/and the necessary Apache configuration in/etc/httpd/conf.d/shib.conf - shibd will be installed to
/usr/sbinand may be managed using/sbin/serviceand/sbin/chkconfig - An appropriate version of
mod_shiband other pluggable modules will be installed to/usr/lib/shibboleth/ - Logs will be located in
/var/log/shibboleth/shibd.log
The installation directory structure may vary depending upon the OS version/type you are using. It might happen that some of the folders/files mentioned above might not be present in your file system. In my case, I was not able to see /etc/httpd/conf.d/shib.conf file . If same thing happens with you, then make all apache related configurations in apache2.conf file as per the apache installation directory structure in your system.
-
Initial testing can be done by hitting the URL http://localhost/Shibboleth.sso/Status .
-
Make Apache aware of Shibboleth
Tell apache where to find the mod_shib you just installed (assuming you are using Apache 2.2). Add the below line in apache2.conf file.
LoadModule mod_shib /usr/lib/apache2/modules/mod_shib_22.so
Note : (For CQ only ) If you have enabled dispatcher, make sure you specify the above line before dispatcher loading i.e. shibd should load before dispatcher gets load.
-
Configuration of Shibboleth SP and providing it to IdP.
The way shibboleth works is by running a daemon called shibd at the same time apache runs, and then mod_shib.so knows how to talk to shibd.
-
Configure
/etc/shibboleth/shibboleth2.xmlThis file tells
mod_shibandshibdall about your setup. It is probably already full of data, but be careful – you need to configure it to know which IdP you’re connecting to. Take a backup of the original file before directly editing this one.-
Make sure the ‘entityID’ points at your machine. Update the
entityIDin<ApplicationDefaults>tag as follows . (You can provide your own ID as well)<ApplicationDefaults REMOTE_USER="eppn persistent-id targeted-id" entityID="http://<your domain>/shibboleth">
I’ll be using http://my.domain.com/shibboleth as the Entity Id.
- Configure the IdP you want to use. Provide the entity ID of the IdP configured in part I or you can simply copy the entity ID present in
<SAML_IDP_HOME>/metadata/idp-metadata.xmlfile
<SSO entityID="https://idp.intelligrape.com/idp/shibboleth">SAML2 SAML1</SSO>
- Also, specify from where the IdP’s metadata will come from. At the IdP server , copy its metadata file
idp-metadata.xmllocated at<SAML_IDP_HOME>/metadatadirectory and place it at your SP server at location/etc/shibboleth/directory. Add the below tag in/etc/shibboleth/shibboleth2.xmlif not already present.
<MetadataProvider type="XML" file="idp-metadata.xml"/>
-
- Configure SP’s Metadata file
-
If you read the instructions at the shibboleth site they seem to VERY STRONGLY IMPLY that you need to construct your own Metadata file for an SP. It is PARTLY true. To start off with, let http://my.domain.com/Shibboleth.sso/Metadata provide a Metadata file for you.
shibdwill create one on-the-fly and serve it to you automatically. - Copy and paste the contents in a file say
sp-metadata.xml. Save this file to the location<SAML_IDP_HOME>/metadata. Once you create or acquire metadata for SP, you must supply it to the IdP. Similarly, the IdP MUST supply its metadata to the SP which was already done in the previous step. -
At IdP server add the following to the
relying-party.xmlfile (at <SAML_IDP_HOME>/conf/) just after the IdP’s own metadata is defined:<pre><metadata:MetadataProvider xsi:type="FilesystemMetadataProvider" xmlns="urn:mace:shibboleth:2.0:metadata" id="SPMETADATA" metadataFile="<SAML_IDP_HOME>/metadata/sp-metadata.xml"/></pre>
-
- In relyingParty.xml, we need to specify the details of IdP’s metadata and any other service provider’s metadata file that relies on our IdP. IdP’s metadata file is already provided in Part I. While specifying the relying party and metadata of SP, value of Provider attribute in
<rp:RelyingParty>tag should be the same as that of EntityId specified in above metadata file. Also, changeencryptAssertionsattribute to “never”.
<rp:RelyingParty id="my.domain.com" provider="http://my.domain.com/shibboleth" defaultSigningCredentialRef="IdPCredential" defaultAuthenticationMethod="urn:oasis:names:tc:SAML:2.0:ac:classes:PasswordProtectedTransport"> <rp:ProfileConfiguration xsi:type="saml:SAML2SSOProfile" inclu deAttributeStatement="true" assertionLifetime="PT5M" assertionProxyCount="0" signResponses="never" signAssertions="always" encryptAssertions="never" encryptNameIds="never" includeConditionsNotBefore="true"/> <rp:ProfileConfiguration xsi:type="saml:SAML2ArtifactResolutio nProfile" signResponses="never" signAssertions="always" encryptAssertions="never" encryptNameIds="never"/> </rp:RelyingParty>
- Modify the
/etc/shibboleth/attribute-map.xmlfile to have list of all the attributes being released from IdP. There are already a lot of attributes mentioned in the file but are commented out. You can find out your own attribute and uncomment it or you can use the below.
<Attribute name="urn:mace:dir:attribute-def:uid" id="uid"/>
8. Protecting and accessing the CQ published resource.
-
In apache2.conf , enable the dispatcher if not already enabled. You can refer the existing documentation or this excellent blog can be followed.
-
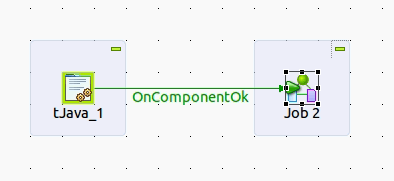
We can use shibboleth to secure the published content. Only authenticated users can access a resource , otherwise the request should not be processed. Below is the block diagram for how the request is processed.
-
In order to check that SP is working, protect a directory by acquiring a shibboleth session. Add the below in
shib.conf(if present in your system) , otherwise you can specify the same inhttpd.conffile. For ubuntu , you can specify it in the file where virtual hosts entries are present. In my case it was/etc/apache2/sites-available/default. It may vary depending upon the installation structure.<Location /path/to/secure/content> # this Location directive is what redirects apache over to the IdP. AuthType shibboleth ShibRequestSetting requireSession 1 require valid-user </Location>
Note that the path mentioned in Location element is relative to the Directory root. A sample configuration can be found at the end of the document.
- Try to access the published page , you should be presented with a IDP login page. Pass the valid credentials to access the page.
-
Note that this configuration can be used to protect any cached website/directory. This implementation is not just limited to CQ.
Troubleshooting :
-
Please make sure to restart tomcat to reflect the changes you do in IdP’s configuration files. For starting/shutting tomcat , go to <TOMCAT_HOME>/bin and run the startup.sh/shutdown.sh respectively.
-
Restart apache server after every change in the apache.conf files.
-
If you have enabled dispatcher module for CQ, make sure you enable it for CQ cached directory only to avoid unwanted errors.
<Directory /path/to/CQ/cached/content> <IfModule disp_apache2.c> SetHandler dispatcher-handler </IfModule> Options FollowSymLinks AllowOverride None </Directory>
-
When you access the published page, make sure not to specify the port no <4503>.
-
Sample Virtual Host Entry in apache configuration .
<VirtualHost *:80> ServerAdmin webmaster@localhost ServerName publish.intelligrape.com DocumentRoot /var/cache/apache2/cq-cache <Directory /> Allow from all Options FollowSymLinks MultiViews AllowOverride None </Directory> <Location /content> AuthType shibboleth ShibRequireSession On require valid-user </Location> ErrorLog ${APACHE_LOG_DIR}/error.log LogLevel warn CustomLog ${APACHE_LOG_DIR}/access.log combined </VirtualHost>Reference Links
http://csrdu.org/blog/2011/07/04/shibboleth-idp-sp-installation-configuration/
http://www.jeesty.com/shibboleth
https://wiki.shibboleth.net/confluence/display/SHIB2/Installation
http://www.switch.ch/aai/support/serviceproviders/sp-access-rules.html
-
P.S. This post was originally published on my company’s website.
Hope it helps !! 🙂